Risk Level: High
Description:
This plugin checks whether TCP or UDP port 53 for DNS is accessible to the public. While some ports, such as HTTP and HTTPS, must be exposed to the public in order to function, other sensitive services, like DNS, should be limited to known IP addresses. If the accessibility of the IP addresses is not kept in check it could make the account vulnerable to attacks.
PingSafe strongly recommends restricting TCP and UDP port 53 to known IP addresses.
About the Service :
In an Azure virtual network, a network security group may be used to restrict network traffic to and from Azure resources. A network security group is a collection of security rules that allow or disallow incoming and outgoing network traffic to and from various Azure services. Source and destination, port, and protocol can all be specified for each rule.
Impact :
Unrestricted ports can make the account vulnerable to attacks. This could lead to the accessibility of sensitive data to the people it’s not meant to be accessible by. If we do not restrict TCP and UDP port 53 to known IP addresses the best security practices will not be followed and attacks can happen.
Steps to reproduce :
- Sign in to your Azure portal with your Azure account.
https://portal.azure.com/#home
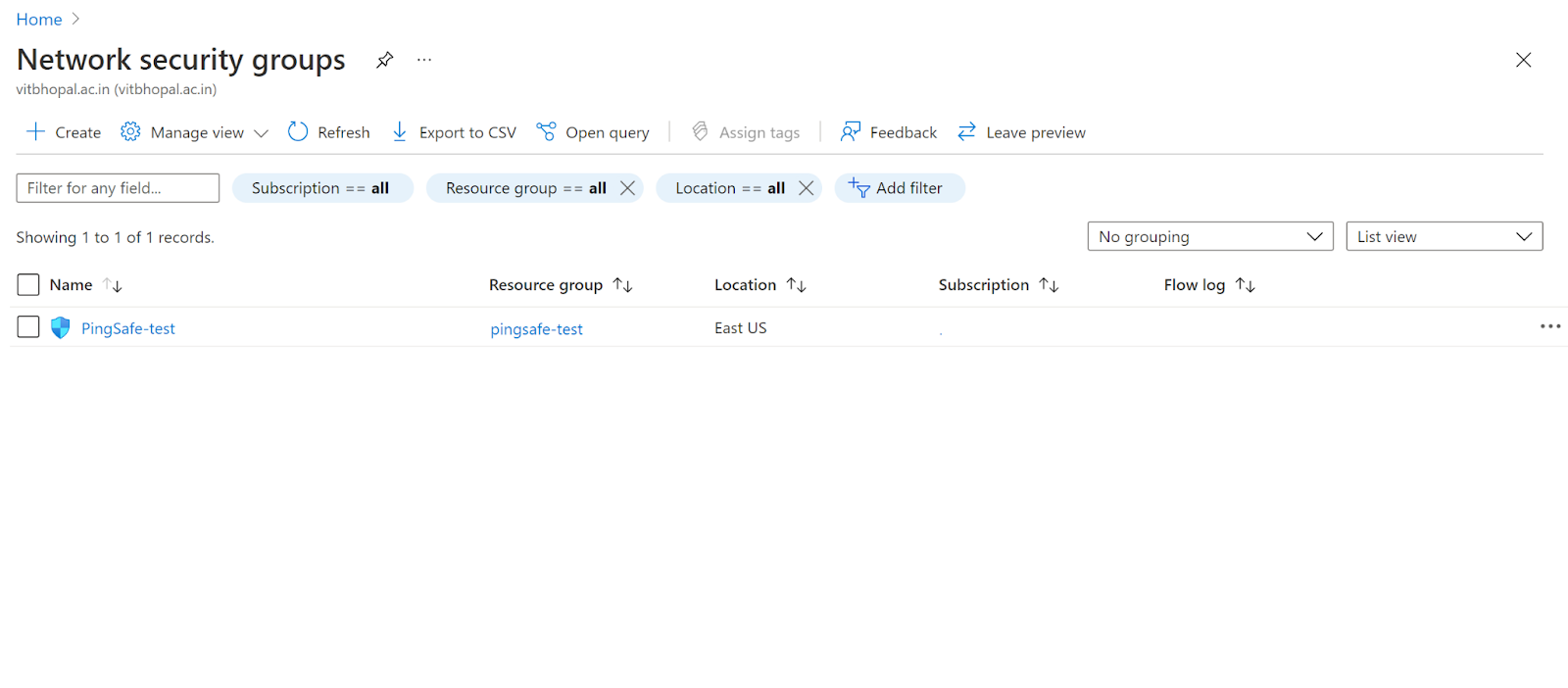
- Navigate to Azure’s Network Security Groups.
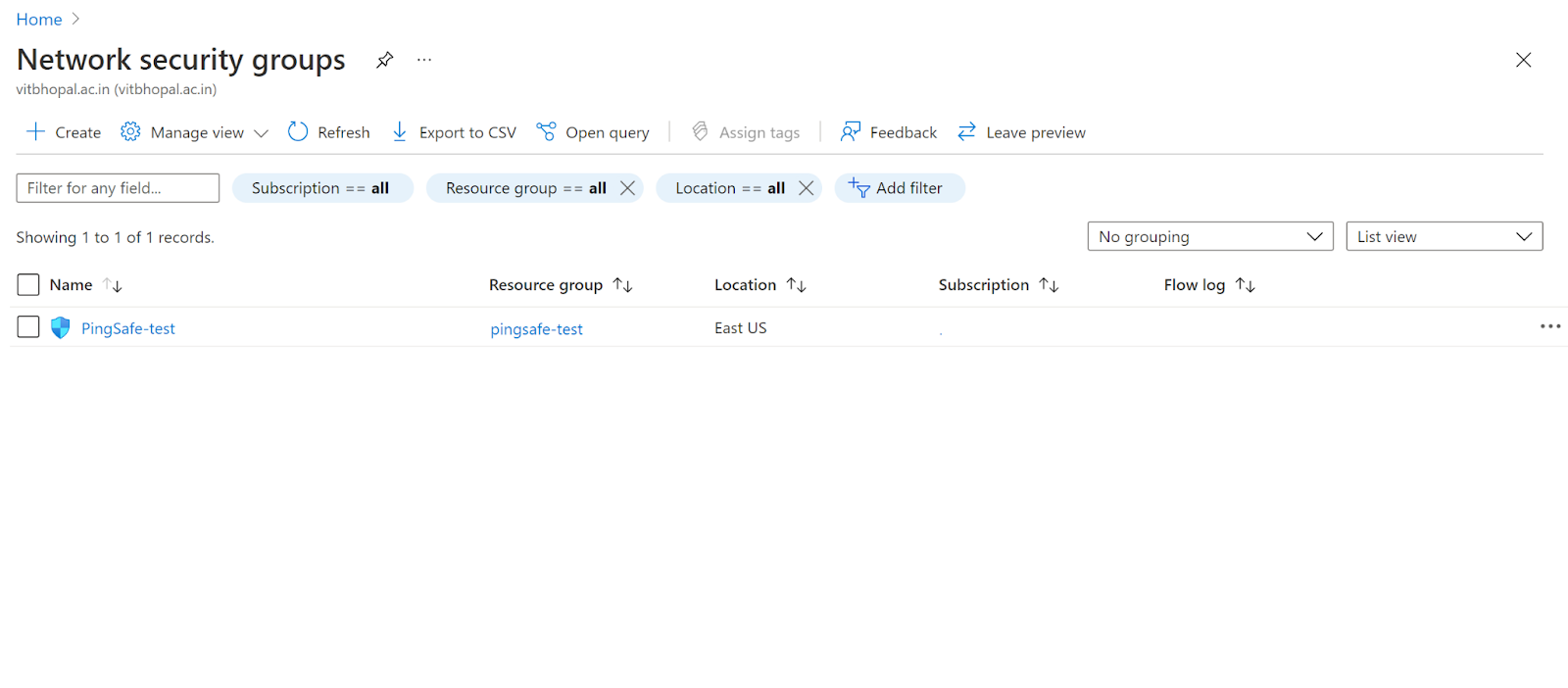
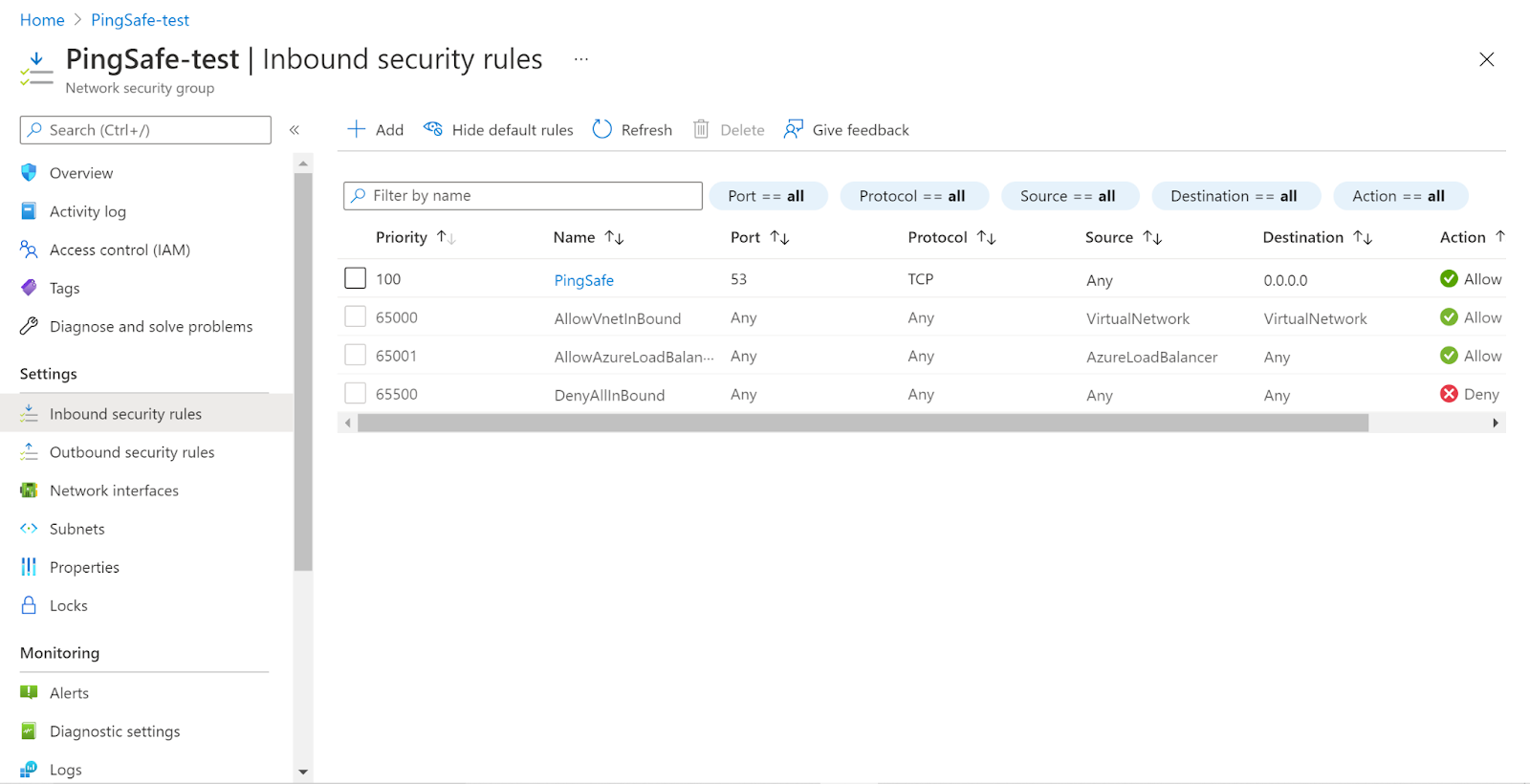
- Click on the Security Group that you want to examine. Next, click on the inbound security rules.
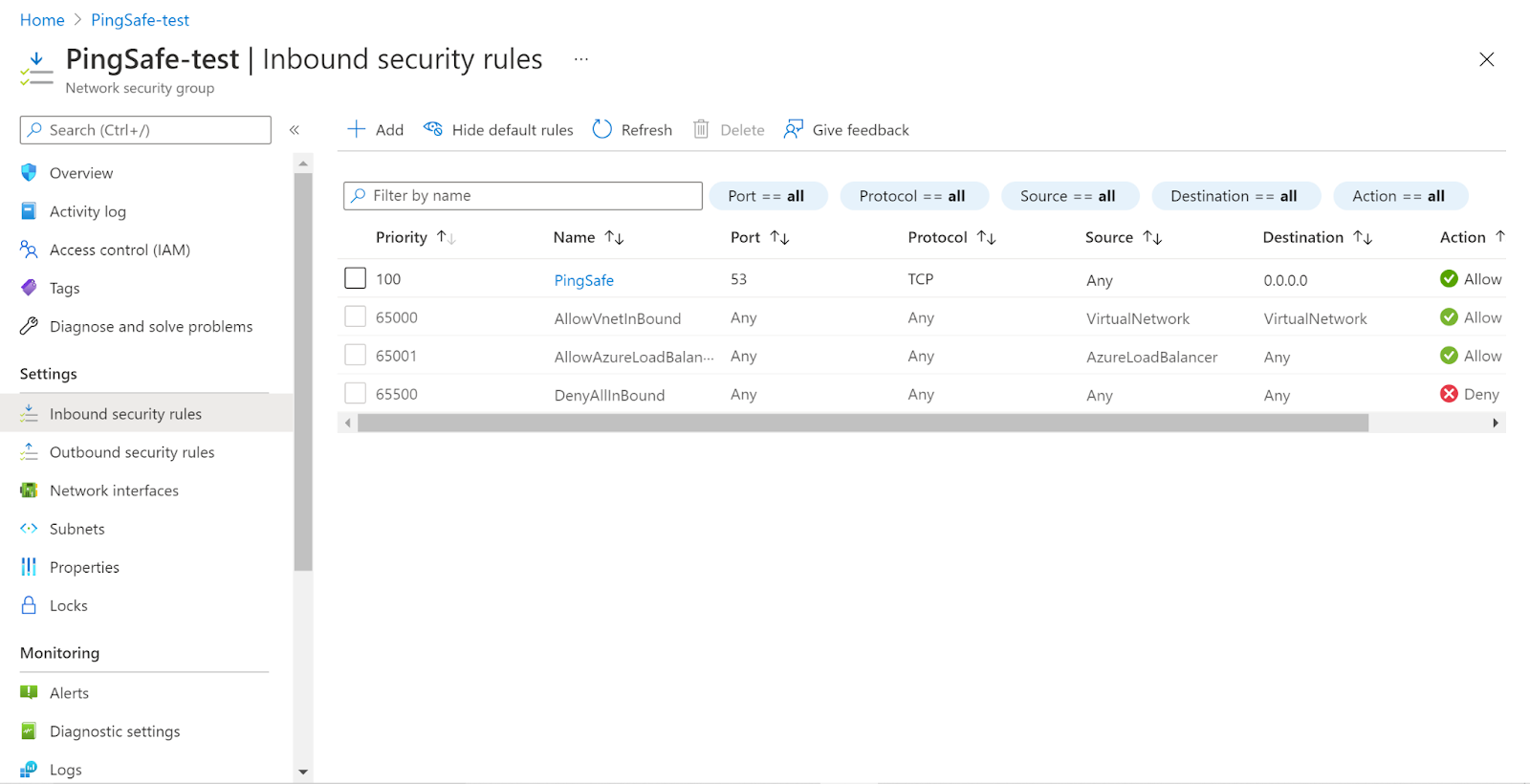
- Check whether TCP or UDP port 53 for DNS is accessible to the public or not. If it shows ANY for Source and Destination that means it is exposed to the public.
- Follow the same steps for other security groups as well.
To check if TCP or UDP port 53 is accessible to the general public or not we examined the port Inbound Security Rules.
Steps for remediation :
- Sign in to your Azure portal with your Azure account.
https://portal.azure.com/#home
- Navigate to Azure’s Network Security Groups.
- Click on the Security Group that you want to examine. Next, click on the inbound security rules.
- Check whether TCP or UDP port 53 for DNS is accessible to the public or not. If it shows ANY for Source and Destination that means it is exposed to the public.
- Next, click on the security group rule and modify the Source from ANY to specific IP addresses or select Application security group and click Save.
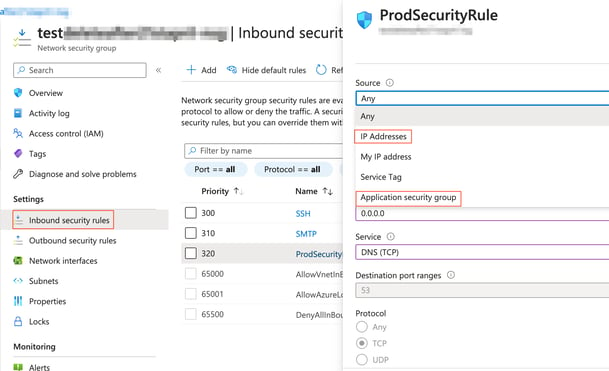
- Now the TCP or UDP port 53 for DNS is not accessible by the public.
- Follow the same steps for other security groups as well.
References :
Please feel free to reach out to support@pingsafe.com with any questions that you may have.
Thanks
PingSafe Support
