Risk Level: High
Description
This plugin determines if the TCP port 22 for the SSH (Secure Socket Shell) is open to the public. Unlike HTTP and HTTPS, which can be available to public access, SSH ports must be restricted to known IP addresses. TCP port 22 is used to connect to SSH servers for remote access. To minimize false positives, this plugin reports only those firewalls with public IP associated with any of its networks.
About the Service
Digital Ocean Firewall:
DigitalOcean Cloud Firewalls are an organization-based, stateful firewall administration for Droplets given at no extra expense. Cloud firewalls block all traffic that isn't explicitly allowed by a standard. Firewalls place an obstruction between your servers and different machines in the organization to safeguard them from outer assaults. Firewalls can behave based, which are designed on a for every waiter premise utilizing administrations like IPTables or UFW. Others, such as DigitalOcean Cloud Firewalls, are network-based and stop traffic at the organization layer before it arrives at the server.
Impact
Firewalls for the droplets are used to control the incoming and outgoing traffic. There are rules defined under firewalls that can allow specific IP addresses to access the droplets with the protocol and the Ports specified. SSH or Secure Shell allows systems to remotely connect to a server or host, allowing them to execute a number of commands and move files. With SSH an encrypted connection is established over an insecure network. But with advanced tools, attackers can brute force username and password credentials to log in to open SSH servers. Gaining SSH server access can enable attackers to steal important information, clone the database or completely wipe off files from servers.
Steps to Reproduce
Using Digital Ocean Console-
In order to determine if your Digital Ocean Firewall Rules permit access without restrictions on TCP port 22, follow the steps mentioned below:
- Firstly use the administrator account for signing in to Digital Ocean Console. A dashboard will appear on the screen.
- Now, from the left Navigation Panel select the name of the Project you want to investigate in.
- After selecting the Project, under the Manage section in the left navigation panel, click on the Networking blade.
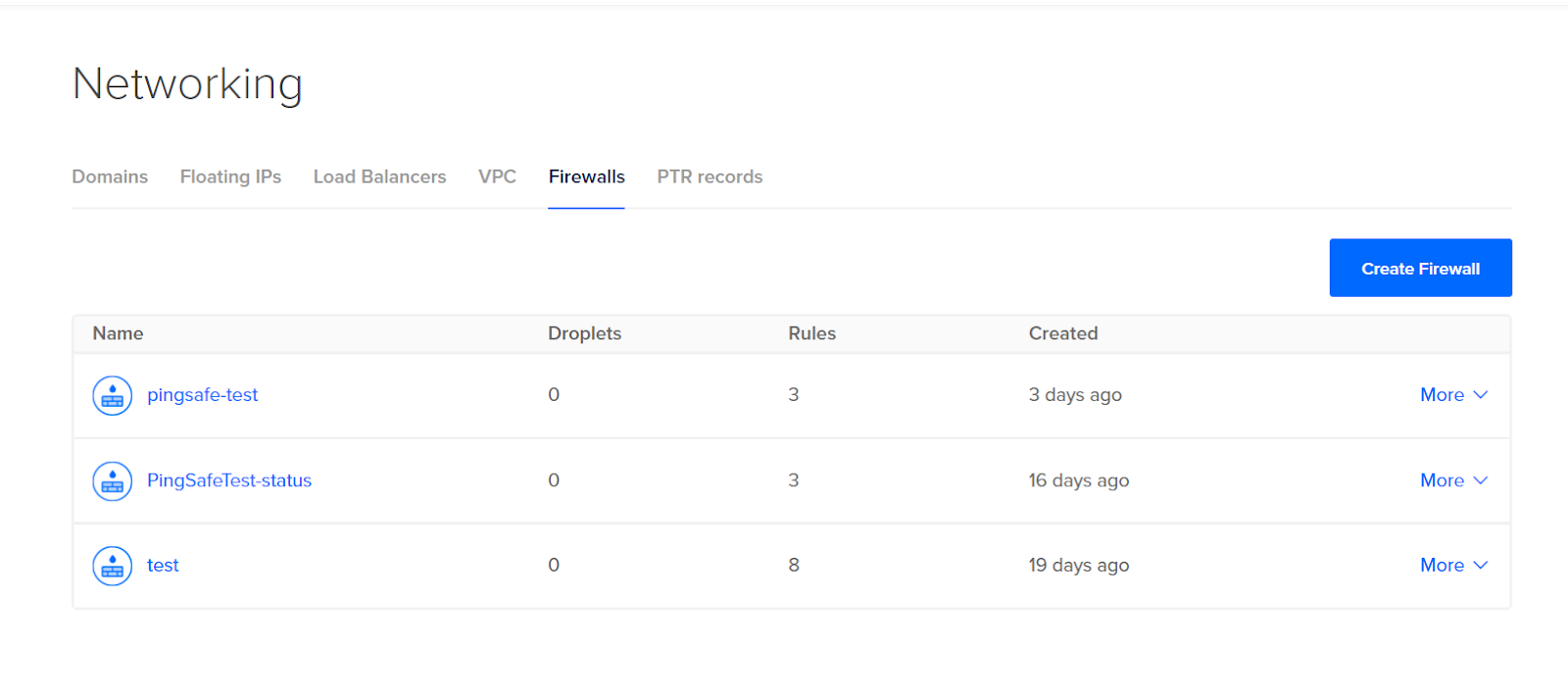
- A Networking page will appear on the screen, select the Firewall tab from the top navigation bar.
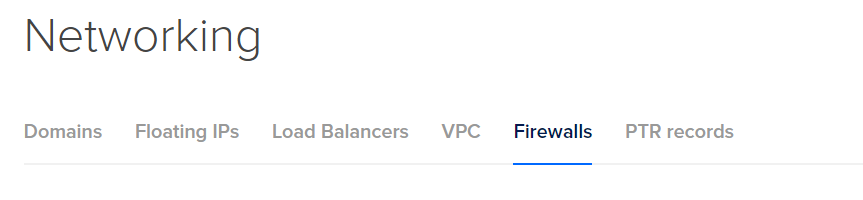
- A Firewall Dashboard will appear on the screen with a list of all the Firewalls available in the current project.
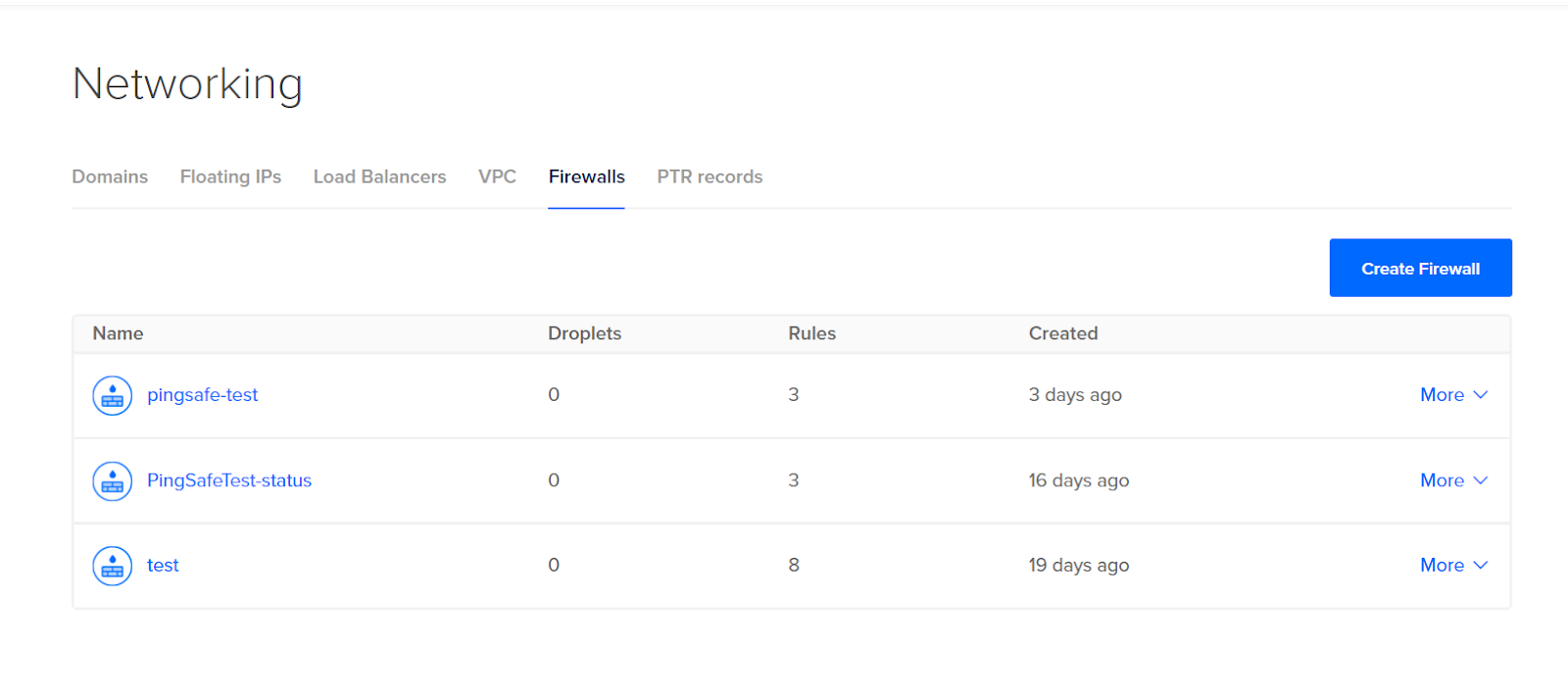
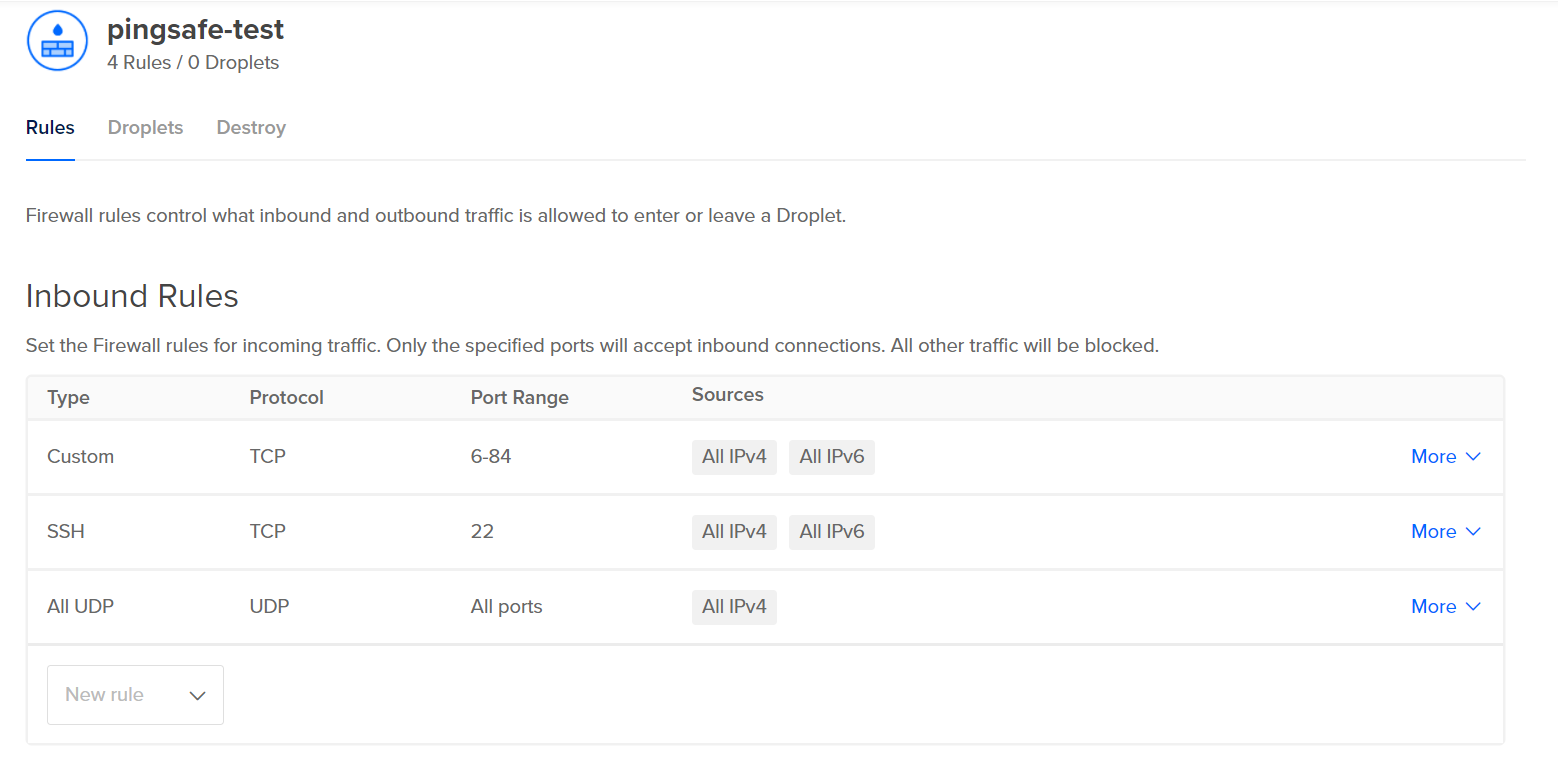
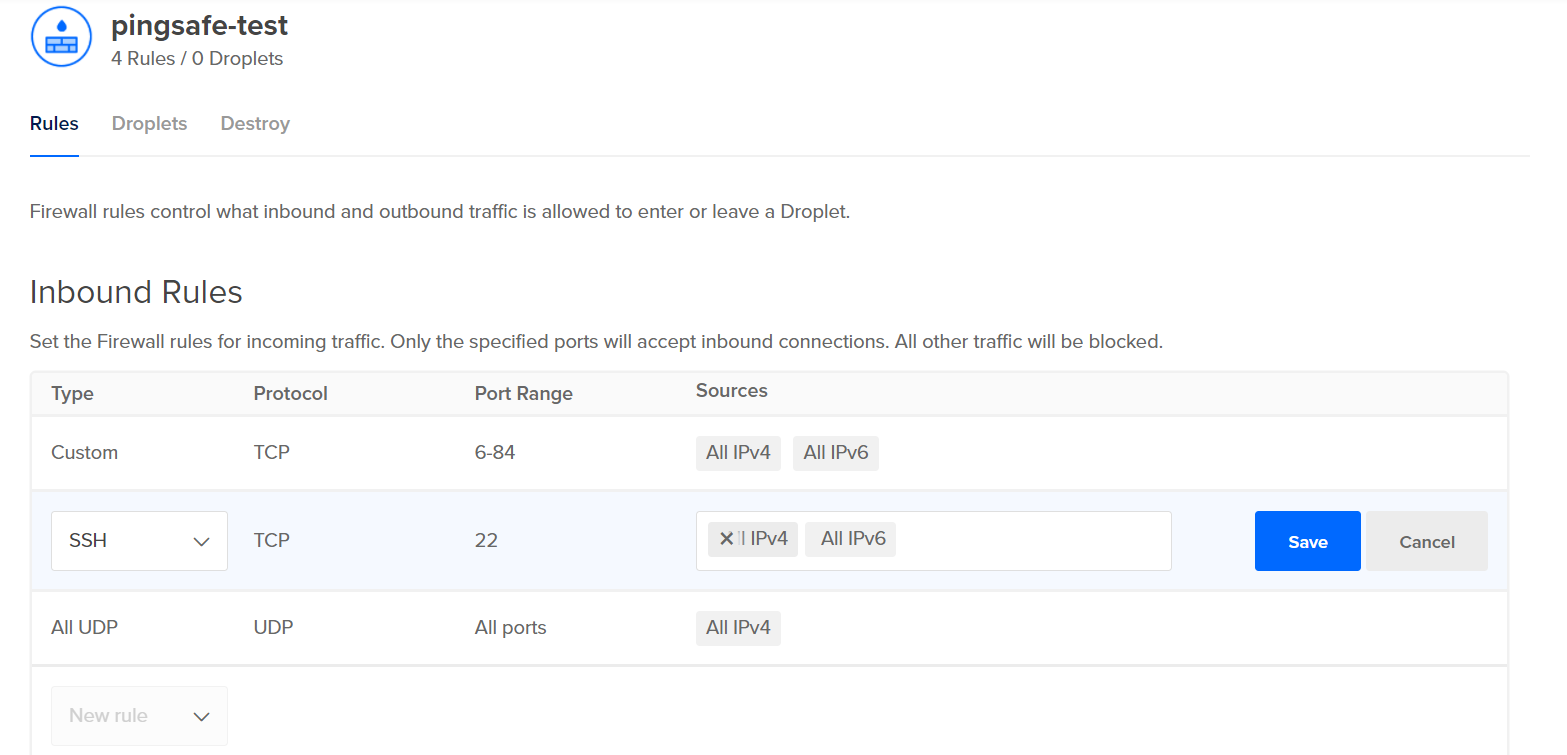
- Click on the name of the firewall you want to investigate in. A new Firewall Page with all the details of inbound and outbound rules will appear on the screen.
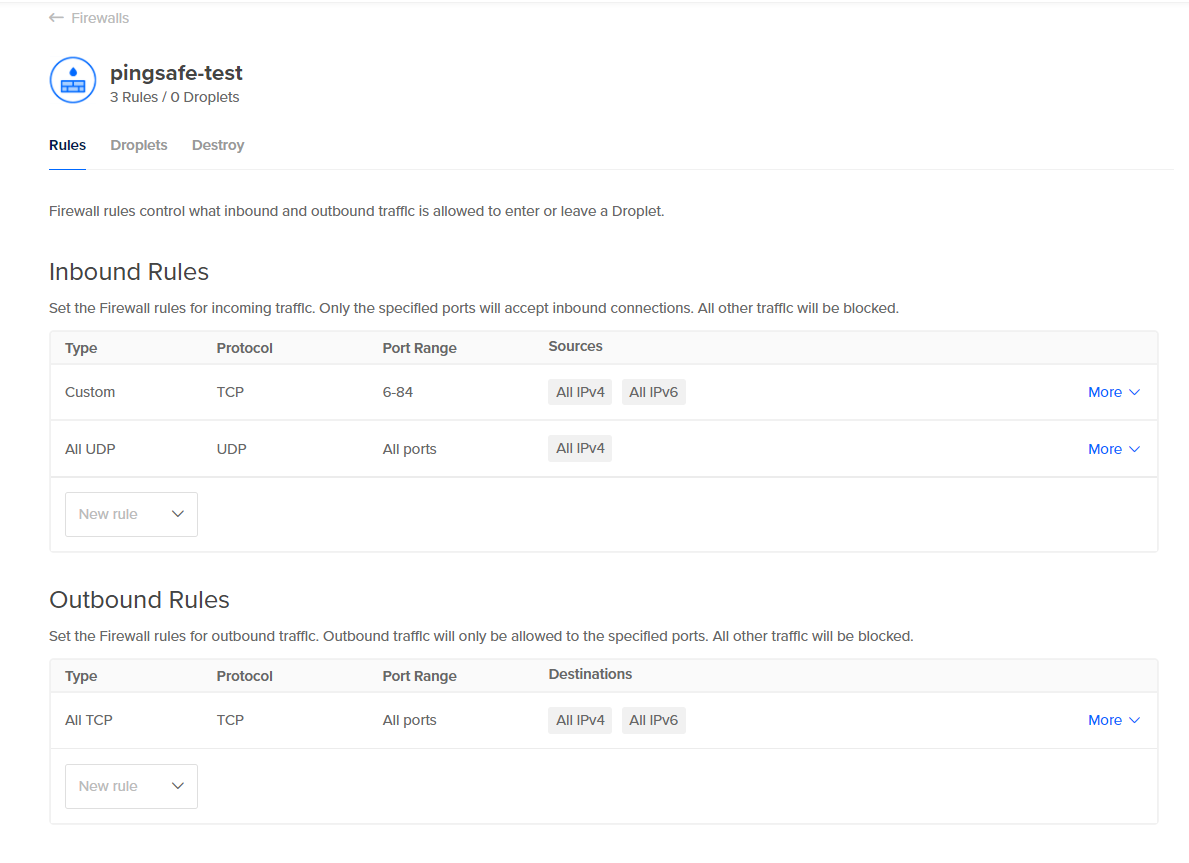
- Check among the list of Inbound Rules if you may find any Firewall Rule with Type: Custom/All TCP, Protocol: TCP, and Port: 22 then this shows that there exist firewall rules that allow unrestricted access on Port 22, hence it is vulnerable as Port TCP 22 for VNC Server is open to the public.
- Check out the Steps for Remediation to fix this issue.
- Repeat the steps mentioned above for reviewing accounts in other folders/projects associated with other Digital Ocean organizations deployed within your record.
Steps for Remediation
In order to update or reestablish your VPC network firewall rules configuration to restrict VNC Server access for trusted authorized IP addresses or IP ranges only, follow the steps given below:
- Firstly use the administrator account for signing in to Digital Ocean Console. A dashboard will appear on the screen.
- Now, from the left Navigation Panel select the name of the Project you want to investigate in.
- After selecting the Project, under the Manage section in the left navigation panel, click on the Networking blade.
- A Networking page will appear on the screen, select the Firewall tab from the top navigation bar.
- A Firewall Dashboard will appear on the screen with a list of all the Firewalls available in the current project.
- Click on the name of the firewall you want to investigate in. A new Firewall Page with all the details of inbound and outbound rules will appear on the screen.
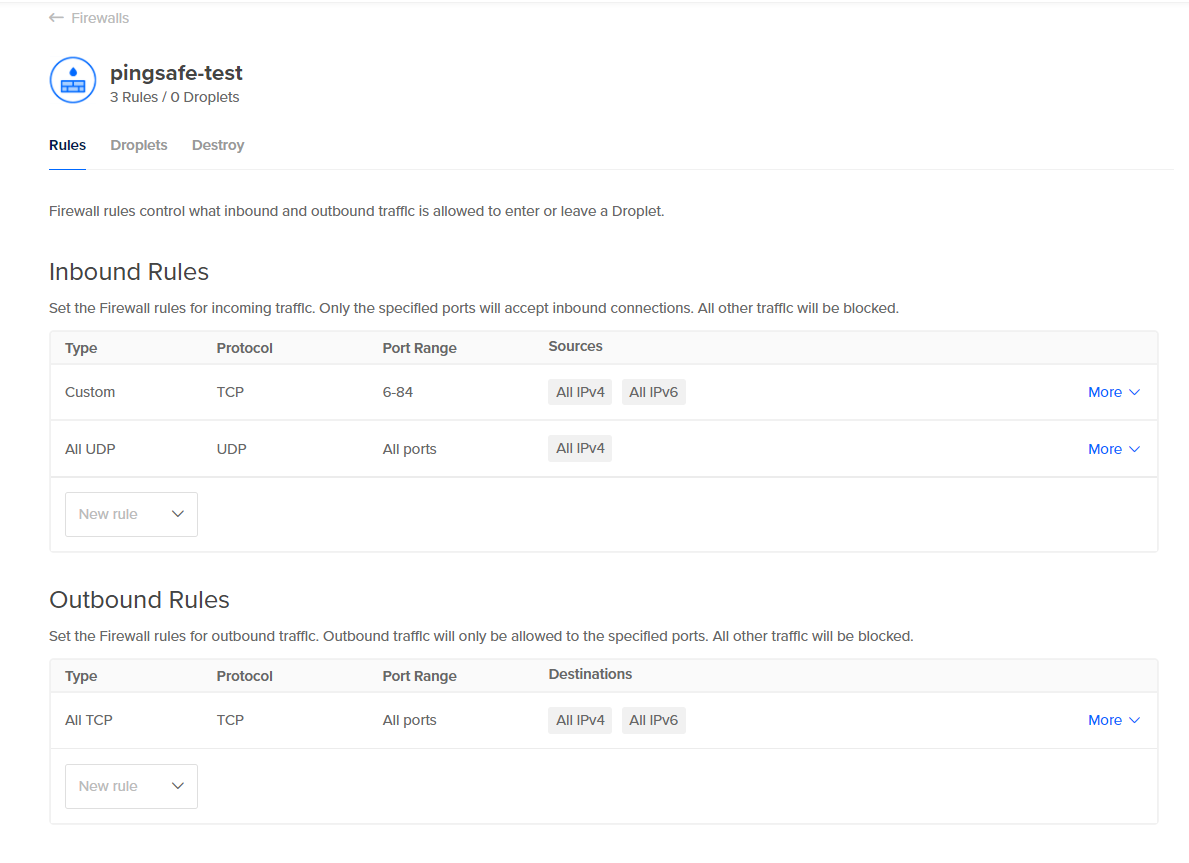
- Check among the list of Inbound Rules if you may find any Firewall Rule with Type: Custom/All TCP, Protocol: TCP, and Port: 22 then this shows that there exist firewall rules that allow unrestricted access on Port 22, hence it is vulnerable as Port TCP 22 for VNC Server is open to the public.
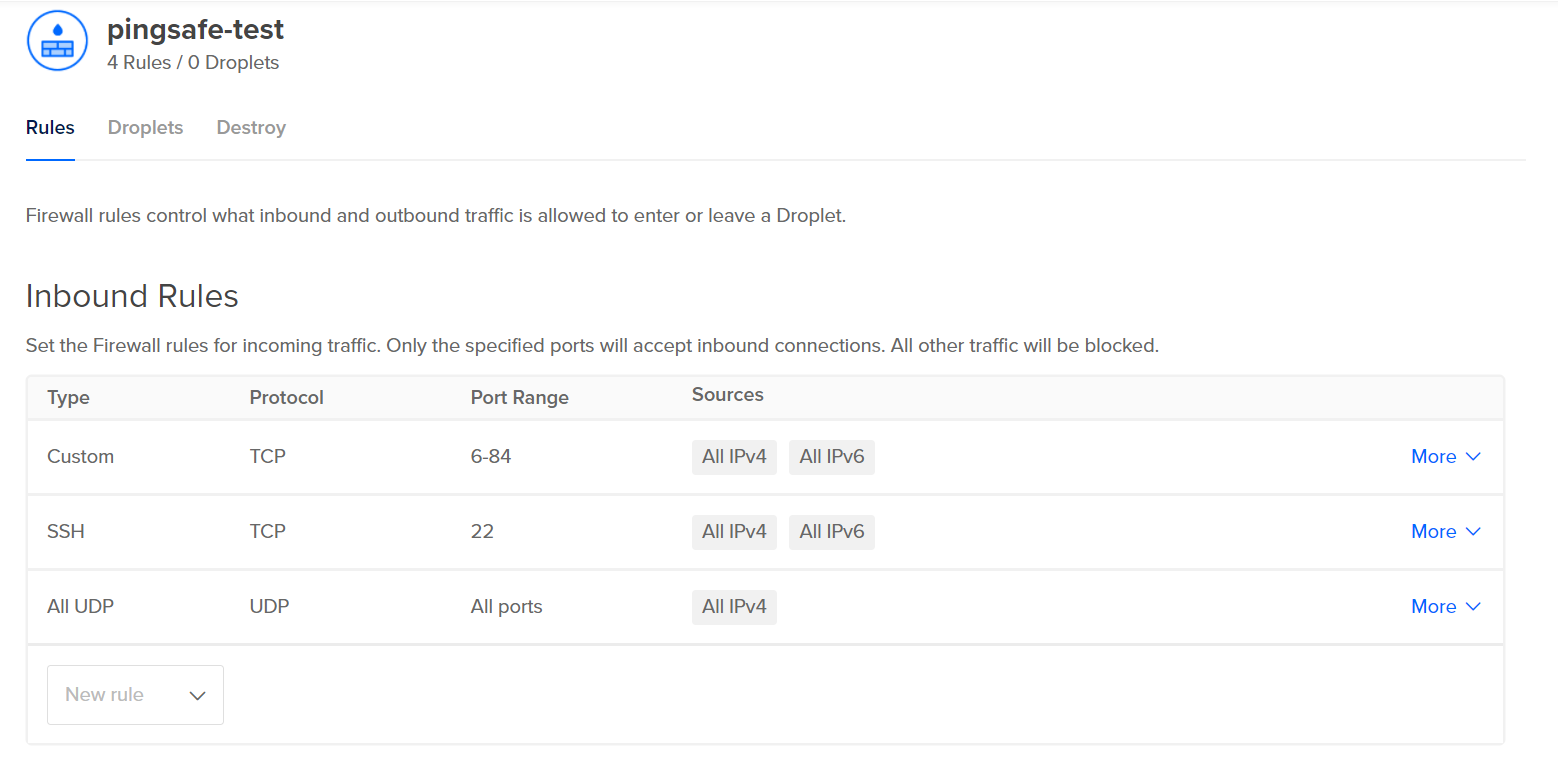
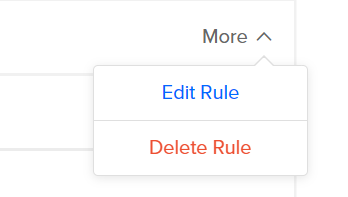
- Click on the Edit Rule button available on the right under the More dropdown link.
- Remove the non-compliant or non-biddable 0.0.0.0/0 IP address range under the Source IP ranges configuration section. This is done to deny public inbound access on port:22 of TCP in the VNC Server.
- Now, type the IP address ranges into the Source IP ranges configuration section. The entered IP address range must be in desired CIDR format like 10.128.0.0/9. The IP range can have addressed included in your VPC network and even outside of your network.
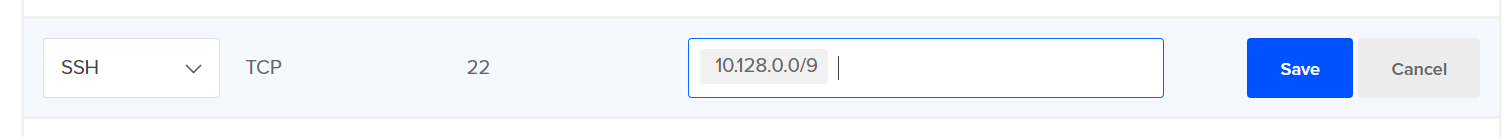
- Now click on the Save button to apply the changes done so far.
- You may repeat steps 7-11 for other firewall rules with TCP port: 22 in your Digital Ocean Project.
- You may repeat the above steps for other Digital Ocean Projects under your organization.
