Risk Level: Medium
Description
This plugin ensures Redshift clusters are not configured to encrypt using default KMS keys. Encryption is an important property from the security aspect. It is recommended to use customer-managed keys instead of default keys to have more flexibility.
About the Service
Amazon RedShift: Amazon RedShift is a data warehouse with fast and secure data analyzing features. It is a powerful and robust service powered by Amazon to run SQL queries and even deploy ML (Machine Learning) models on the data. For additional monitoring benefits, it also provides access to real time operational analytics.
Impact
It is highly recommended to encrypt your Amazon RedShift data.
It is highly recommended to properly encrypt Redshift clusters with customer-managed KMS keys. AWS Customer managed keys provide better flexibility to increase encryption level and thus, deliver better security for clusters. The default keys provide a minimal level of security.
Steps to Reproduce
Using AWS Console-
- Log In to your AWS Console.
- Open the Amazon RedShift Console. You can use this link (https://console.aws.amazon.com/redshiftv2/) to navigate directly if already logged in.
- From the left navigation pane, click on Clusters.
- A list of clusters will be displayed. Select the cluster you want to examine by clicking on it’s Cluster Name.
- Move to the Properties tab.
- If the Encryption is enabled, copy the AWS KMS Id.
- Move to the AWS KMS console to check if the key exists. (https://console.aws.amazon.com/kms/) Make sure you are in the same region as that of the cluster.
- From the left navigation pane, select the AWS-managed-keys section.
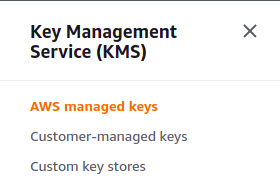
- Paste the key ARN copied in the search bar. If the key is found, the vulnerability exists.
- Repeat steps for all the clusters you wish to examine.
Steps for Remediation
Update Redshift clusters encryption configuration to use KMS CMKs instead of AWS managed-keys.
- Log In to your AWS Console.
- Open the Amazon RedShift Console. You can use this link (https://console.aws.amazon.com/redshiftv2/) to navigate directly if already logged in.
- From the left navigation pane, click on Clusters.

- A list of clusters will be displayed. Select the vulnerable cluster by clicking on it’s Cluster Name.
- Move to the Properties tab.
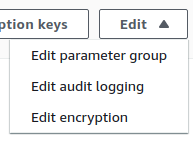
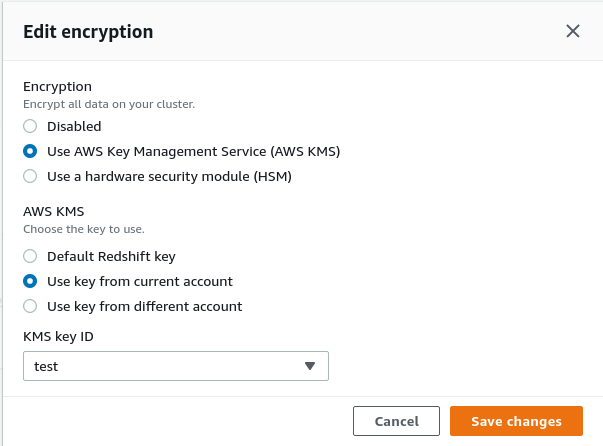
- From the Edit drop down menu in the top-right corner, select Edit encryption option.
- Choose a valid CMK-KMS key Id from the drop down list and click on Save changes when done.
- Repeat steps 3 to 8 for all the vulnerable clusters.
